NTLM vs KERBEROS
(WWW)
Podemos interpretar este post como os três W's, um para cada capítulo.
Vamos passar pelos conceitos basicos do NTLM e do Kerberos. Quais são as principais diferenças entre eles, como funciona o fluxo e como podemos identificar qual protocolo está sendo usado.
Então, sem mais demora. Aqui vai a história ...
Capítulo 1
The What:
O que é o NTLM?
O NTLM é um protocolo de autenticação. Era o protocolo padrão usado nas versões antigas do Windows, mas ainda é usado hoje. Se por algum motivo o Kerberos falhar, o NTLM será usado.
O NTLM possui um mecanismo de desafio / resposta.
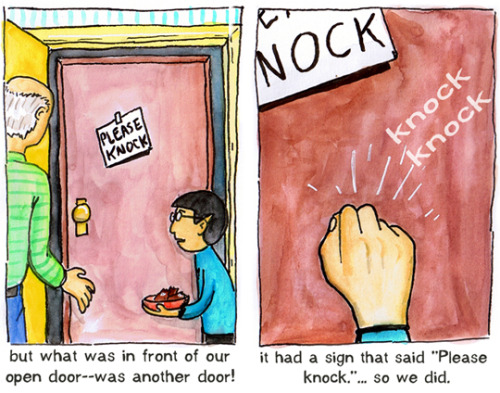
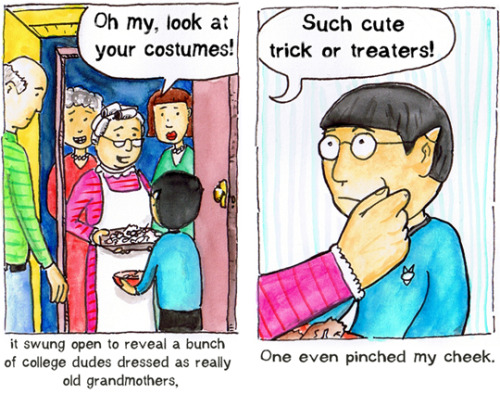
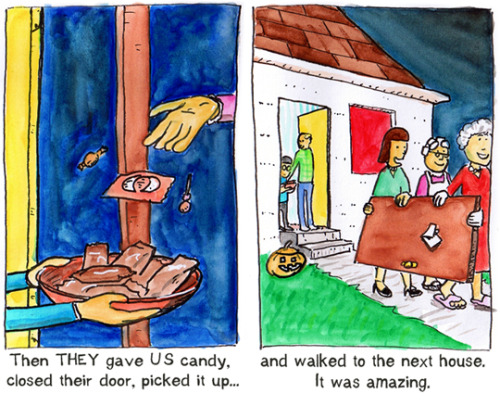
Aqui está como funciona o fluxo NTLM:

1 - Um usuário acessa um computador cliente e fornece um nome de domínio, um nome de usuário e uma senha.
O cliente calcula um hash criptográfico da senha e descarta a senha real. O cliente envia o nome do usuário para o servidor (em texto sem formatação).
2 - O servidor gera um número aleatório de 16 bytes, chamado desafio, e o envia de volta ao cliente.
3 - O cliente criptografa esse desafio com o hash da senha do usuário e retorna o resultado para o servidor. Isso é chamado de resposta.
4 - O servidor envia os três itens a seguir para o controlador de domínio:
- Nome do usuário
- Desafio enviado ao cliente
- Resposta recebida do cliente
5 - O controlador de domínio usa o nome de usuário para recuperar o hash da senha do usuário. Ele compara o desafio criptografado com a resposta do cliente (na etapa 4). Se eles forem idênticos, a autenticação será bem-sucedida e o controlador de domínio notificará o servidor.
6 - O servidor envia a resposta apropriada de volta ao cliente.
O que é o Kerberos?
O Kerberos é um protocolo de autenticação. É o protocolo de autenticação padrão nas versões do Windows acima do W2k, substituindo o protocolo de autenticação NTLM.
Aqui está como o fluxo do Kerberos funciona:

1 - Um usuário loga na máquina cliente. O cliente faz um pedido de texto simples (TGT). A mensagem contém: (ID do usuário; ID do serviço solicitado (TGT); O endereço de rede do cliente (IP); tempo de vida da validação)
2 - O servidor de autenticação verificará se o usuário existe no banco de dados do KDC. Se o usuário for encontrado, ele gerará aleatoriamente uma chave (chave de sessão) para uso entre o usuário e o Servidor de Concessão de Ticket (TGS). O servidor de autenticação enviará duas mensagens de volta para o cliente: - Um é criptografado com a chave secreta do TGS. - Um é criptografado com a chave secreta do cliente.
NOTA: A chave de sessão TGS é a chave compartilhada entre o cliente e o TGS. A chave secreta do cliente é o hash das credenciais do usuário (nome de usuário + senha).
3 - O cliente descriptografa a chave e pode fazer logon, fazendo o cache localmente. Ele também armazena o TGT criptografado em seu cache. Ao acessar um recurso de rede, o cliente envia uma solicitação ao TGS com o nome do recurso que ele deseja acessar, o ID do usuário / registro de data e hora e o TGT em cache.
4 - O TGS descriptografa as informações do usuário e fornece um tíquete de serviço e uma chave de sessão de serviço para acessar o serviço e enviá-lo de volta ao Cliente depois de criptografado.
5 - O cliente envia o pedido para o servidor (criptografado com o tíquete de serviço e a chave de sessão)
6 - O servidor descriptografa o pedido e, se for genuíno, fornece acesso ao serviço.
Capítulo 2
The When:
Como podemos identificar quando estamos usando o NTLM ou o Kerberos?
Podemos confirmar a autenticação sendo usada pela simples coleta de um Fiddler. No Fiddler, podemos ver os pedidos sendo feitos nos Inspetores / Cabeçalhos:
Kerberos:

NTLM:

Se a solicitação iniciar com o Kerberos e falhar, o NTLM será usado. Podemos ver a resposta nos cabeçalhos também:

Quais são as dependências do Kerberos?
Tanto o cliente quanto o servidor precisam estar executando o W2k ou versões posteriores e estar no mesmo domínio ou confiável.
Um SPN precisa existir no AD para a conta de domínio em uso para executar o serviço no qual o cliente está sendo autenticado.
Capítulo 3
The Why:

Os hashes NTLMv1 podem ser quebrados em segundos com a computação de hoje, pois eles têm sempre o mesmo tamanho e não são salted.
O NTLMv2 é um pouco melhor, desde o tamanho variável e o hash salted, mas não muito melhor. Mesmo que o hash seja salted antes de ser enviado, ele é salvo unsalted na memória de uma máquina.
E claro, quando falamos sobre o NTLM, falamos sobre um mecanismo de desafio / resposta, que expõe sua senha ao cracking off-line ao responder ao desafio.
O Kerberos fornece várias vantagens sobre o NTLM:
- Mais seguro: Nenhuma senha armazenada localmente ou enviada pela rede.
- Melhor desempenho: desempenho aprimorado em relação à autenticação NTLM.
- Suporte à delegação: os servidores podem representar clientes e usar o contexto de segurança do cliente para acessar um recurso.
- Gerenciamento de confiança mais simples: evita a necessidade de ter relações de confiança p2p em ambientes de vários domínios.
- Suporta MFA (Multi Factor Authentication)
O fim
 Que patada! PATAda, entenderam?! HAUHAUHhahah ok, desculpe
Que patada! PATAda, entenderam?! HAUHAUHhahah ok, desculpe 
































 facebook
facebook reddit
reddit
