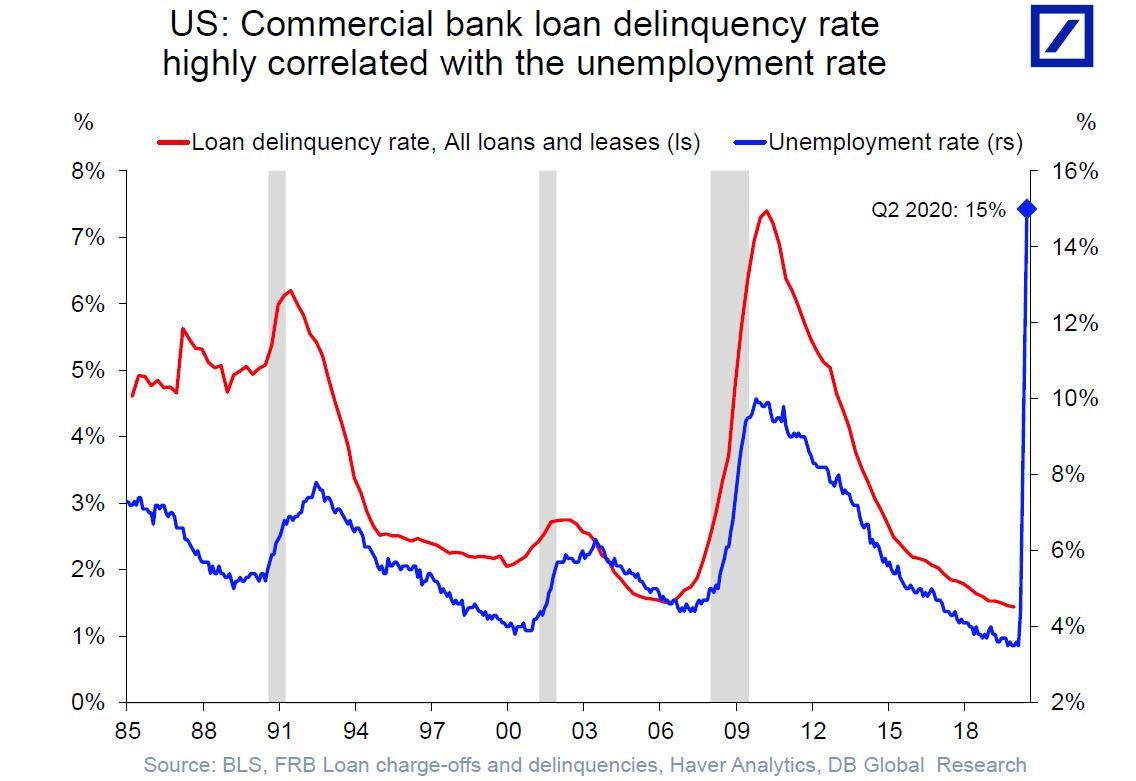
The Leonardo DRS AC²ES Assured Position, Navigation, and Timing solution is driven by the power of the MFoCS system already installed in most tactical vehicles. Photo courtesy of Leonardo DRS.
In this Q&A with William Guyan, senior vice president and general manager of Leonardo DRS Land Electronics, we discuss how AC²ES (A-PNT Converged Computer-Embedded and Scalable) can provide immediate A-PNT capabilities through the Mounted Family of Computer Systems (MFoCS).
Breaking Defense: What’s driving the need for Assured PNT?

William Guyan, Senior Vice President and General Manager, Land Electronics. Photo courtesy of Leonardo DRS.
Guyan: All international forces have become network enabled and GPS dependent. Along with the benefit of using GPS for management of forces and using the timing that comes with GPS in order to synchronize defense systems, comes the downside that someone can take those away from you, as well. Just as there are many systems that enable GPS and networks, now there are new systems that can deny those and create an environment that jams or spoofs GPS signals. Systems that are dependent upon position data or the timing that comes from a GPS satellite network can now be fooled or disabled by an adversary.
Breaking Defense: Are we seeing that happening now, like we’re experiencing on the network side with constant cybersecurity attacks?
Guyan: We’re aware of the capability that our adversaries have, and I think they’ve demonstrated a willingness to use it. It only makes sense, given our dependency on the capabilities that GPS provides, to level the playing field in an area where we have great advantage.
Taking away our ability to know where we are and our ability to synchronize forces using modern systems is something that any adversary would try to do. Because of that, the Army identified this as one of its critical modernization objectives—the need to identify and field an Assured Position, Navigation, and Timing capability, or A-PNT. In fact, one of the cross-functional teams that the Army formed to address key capability gaps and modernization challenges is the A-PNT/Space CFT. So, in addition to having a program of record that’s already delivering A-PNT capability, the Army also has a cross-functional team charged with continuing to identify new ways of fielding new, innovative, and more cost effective capabilities across the force.
Breaking Defense: How is PNT presently supported by MFoCS and how might it evolve with AC²ES?
Guyan: MFOCS is the acronym for the Mounted Family of Computing Systems, the computer and displays systems used by PM Mission Command to enable Joint Battle Command Platform (JBCP) and Mounted Mission Command capabilities. Most of the MFoCS systems that are delivered today are delivered with an embedded anti-spoofing GPS, or a SAASM GPS. There’s a next generation of GPS called an M-Code GPS that is in the pipeline and could be an easy drop-in addition to the MFoCS system to provide for a more resilient, jam-resistant, spoof-resistant capability.
But there are also a whole series of additional capabilities that can be found in the A-PNT toolbox. That’s what we have done with AC²ES, which is a Swiss Army knife of capabilities that will allow a customer to match up their risk profile and their affordability profile with a spectrum of capability choices that best match their needs.
Right now the Army has two choices: standard GPS and the higher-end solution called MAPS (Mounted Assured Precision Navigation and Timing System), which is the Army’s program of record for A-PNT. MAPS works; MAPS is being fielded and it will do the job.
The issue is that MAPS is not going to be immediately, nor affordably, available for all of the systems where we need to have resilient A-PNT. The Army needs additional complementary solutions in addition to MAPS, tier two and tier three solutions, if you will, that allows them to pull left the capability fielding of A-PNT, within budget constraints because you can find a GPS, one or more, on almost every platform, almost every complex system that the Army has. Every one of those systems could be disrupted by an enemy that chooses to do so.
So, in order to be able to fight the way we want to fight – and be able to depend upon the systems that we rely on now, A-PNT at different levels of capability has to be fielded across the force in order to give the enemy reason to be concerned about the effectiveness of their jamming efforts. That may cause them to change the way they fight and, importantly, will also give our soldiers increased assurance and confidence that their systems will work even in non-permissive environments.
Breaking Defense: Does AC²ES provide a different or better capability than MAPS?
Guyan: The AC²ES capability is, we believe, complementary to the capability that the Army already has in the pipeline under the MAPS program. It doesn’t replace MAPS, it doesn’t challenge MAPS. But as a complement to MAPS, it can address the need to field additional systems more quickly and affordably. It provides a spectrum or menu of capability choices that the user can pick from in order to match up how much they need to spend with the risk that they’re trying to avoid.
One way to help the Army and the Marine Corps in pulling this capability left – and doing it affordably – is to allow them the opportunity to reuse the investment they’ve already made in MFoCS hardware. Although AC²ES can be implemented inside of MFoCS hardware as an upgrade, it’s not currently part of the MFoCS program.
More than a billion dollars worth of MFoCS computers have been purchased by the services. We can take the computing power that’s already resident in these installed systems and upgrade them to provide assured position, navigation, and timing capability for Mission Command/Blue Force Tracking, and also distribute the A-PNT data to other systems systems, to make them better protected against the risk of enemy jamming or spoofing.
Breaking Defense: And you funded this with our internal research and development dollars?
Guyan: Yes, we have a very aggressive, self-funded capability development effort inside of Leonardo DRS. This is one of the areas where we saw the customer expressing a need for a capability, and us having the potential for filling that need in a way that adds value. For some customers and certain applications, we saw the opportunity to add capability, save them money, and allow them to deliver the capability more quickly.
In some cases, the customer’s major constraint is not necessarily cost. It could be size, weight, or power. The MFoCS system already has a footprint on most platforms. It already has power and has a space claim, so we’re not adding another box or an installation kit.
We demonstrated AC²ES at the second annual PNT Assessment Exercise (PNTAX) last year and we’ll be demonstrating it again later this month at this year’s PNTAX event, validating its capability at White Sands Missile Range in all of the different capability levels that that we’re trying to offer.
Breaking Defense: What are some of the results and performance that you’ve seen so far?
Guyan: We received very encouraging results from the participation in the last PNTAX, results that were encouraging enough to get the attention of, I think, the CFT and representatives both inside the Army and Marine Corps.
The PNTAX event that we’re doing this year is a more extensive set of testing. It’s being monitored by those customers, who have demonstrated or expressed interest in the product. We see it as a kick-the-tire event for our capability. In addition to being able to evaluate our capability, customers are going to be able to evaluate our capability versus other capabilities and the cost trade-offs associated with them.
One of the interesting things that we are able to do with the AC²ES solution—in addition to bringing capability to the left and saving cost in the fielding—is that we’re also able to combine the A-PNT capability with the computing power that’s resident inside of the MFoCS platform.
This allows us to lean on a wider range of potential solutions for dealing with impaired PNT. One of them is a solution called vision navigation. This is the ability to match up what sensors see on a platform with a one-world-map database to confirm or deny that the positional location coming from the system matches up with what the sensors are seeing. So, it’s a fallback safety to the system because you’re actually matching what the position navigation system is telling you against what the sensors are seeing on the ground.
Again, it’s one further way to check that the GPS data that’s being received is accurate. We’re making good progress in that area and seeing high fidelity. That’s a capability that wasn’t originally designed for AC²ES but because we have the computing power and a very high-end processor that is inside of the MFoCS processor unit, we’ve been able to demonstrate that capability, as well.
That’s one area where we’re demonstrating a capability that MAPS was never asked to demonstrate, but points the way to enhanced capabilities for A-PNT going forward.