Over the last few months we've witnessed a veritable flood of misleading to simply false articles about internet companies showing up in mainstream sources. There were misleading articles in Vox and the Washington Post. And then, just recently, we saw not one but two NY Times pieces that went out of their way to misrepresent the law. And, then of course, there's the Wall Street Journal that has been misrepresenting Section 230 for ages. To date, the only one of these publications to run a serious correction (and to continue to help debunking misrepresentations) is the smallest of those listed above: Vox, who did some research and published a big mea culpa.
This has gotten many in the tech industry to begin to wonder. It's one thing for (cross aisle) grandstanding politicians like Ted Cruz, Josh Hawley, Nancy Pelosi, and Richard Blumenthal to totally misrepresent the law. But when the mainstream media is doing so on a regular basis -- it's causing a lot of talk behind the scenes about whether this is a coordinated hit. Some, like the excellent reporter Anna Wiener, recently more or less dismissed this theory as being "mostly... a facile argument," though I think she mixes up two separate issues. First, it is absolutely true that many startup founders don't know how to deal with the press well, and get personally offended by bad press coverage. And, for those entrepreneurs: fuck 'em. They should grow up and learn what the press actually does, when done right -- which includes researching and debunking nonsense (and there's a ton of nonsense in Silicon Valley).
But, that's a separate issue from whether or not there's a coordinated campaign to undermine the foundations of the internet by a few larger, legacy industries who have failed to adapt to a changing time. Indeed, we saw significant evidence of Hollywood's top lobbyists working behind the scenes (though, it occasionally slipped out publicly) to push for FOSTA, the first bill that significantly undermined Section 230.
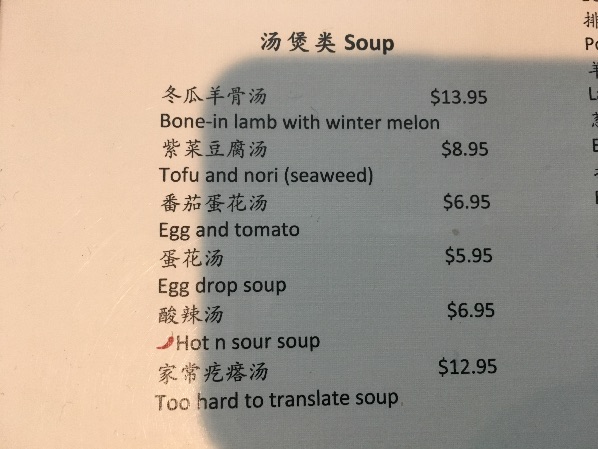
And there's plenty more evidence of legacy industries -- mainly legacy media and entertainment companies -- plotting to take down internet companies by making use of the news. Remember, during the Sony Pictures hack, that MPAA emails were leaked, revealing "Project Goliath," which was specifically a plan to damage Google through any means necessary -- and that included using a smear campaign placed in the Wall Street Journal and on the Today Show. In an email sent to an official in Mississippi Attorney General Jim Hood's office by then MPAA "director of external state government affairs" official (and former ICE official) Brian Cohen, Cohen admits the "proposed plan" is to place an anti-Google smear campaign:
If that image is not showing up, the text comes from a larger strategic plan between the MPAA and various state Attorneys' General, and includes this:
Media: We want to make sure that the media is at the NAAG meeting. We propose working with MPAA (Vans), Comcast, and NewsCorp (Bill Guidera) to see about working with a PR firm to create an attack on Google (and others who are resisting AG efforts to address online piracy). This PR firm can be funded through a nonprofit dedicated to IP issues. The "live buys" should be available for the media to see, followed by a segment the next day on the Today Show (David green can help with this). After the Today Show segment, you want to have a large investor of Google (George can help us determine that) come forward and say that Google needs to change its behavior/demand reform. Next, you want NewsCorp to develop and place an editorial in the WSJ emphasizing that Google's stock will lose value in the face of a sustained attack by AGs and noting some of the possible causes of action we have developed.
So, sure, while it may seem "facile" for some to argue that legacy media firms are out to get big internet companies with trumped up claims in their own media properties, there's very real evidence of a conspiracy to do literally that. Not so facile.
And there's more where that comes from. In Wired's giant profile last year of the "troubles" inside Facebook, it is made clear that Rupert Murdoch used his ability to damage the company via the editorial pages of the WSJ as part of a negotiating strategy:
Zuckerberg traveled to Sun Valley, Idaho, for an annual conference hosted by billionaire Herb Allen, where moguls in short sleeves and sunglasses cavort and make plans to buy each other’s companies. But Rupert Murdoch broke the mood in a meeting that took place inside his villa. According to numerous accounts of the conversation, Murdoch and Robert Thomson, the CEO of News Corp, explained to Zuckerberg that they had long been unhappy with Facebook and Google. The two tech giants had taken nearly the entire digital ad market and become an existential threat to serious journalism. According to people familiar with the conversation, the two News Corp leaders accused Facebook of making dramatic changes to its core algorithm without adequately consulting its media partners, wreaking havoc according to Zuckerberg’s whims. If Facebook didn’t start offering a better deal to the publishing industry, Thomson and Murdoch conveyed in stark terms, Zuckerberg could expect News Corp executives to become much more public in their denunciations and much more open in their lobbying. They had helped to make things very hard for Google in Europe. And they could do the same for Facebook in the US.
.... Inside Facebook, executives believed Murdoch might use his papers and TV stations to amplify critiques of the company. News Corp says that was not at all the case; the company threatened to deploy executives, but not its journalists.
Zuckerberg had reason to take the meeting especially seriously, according to a former Facebook executive, because he had firsthand knowledge of Murdoch’s skill in the dark arts. Back in 2007, Facebook had come under criticism from 49 state attorneys general for failing to protect young Facebook users from sexual predators and inappropriate content. Concerned parents had written to Connecticut attorney general Richard Blumenthal, who opened an investigation, and to The New York Times, which published a story. But according to a former Facebook executive in a position to know, the company believed that many of the Facebook accounts and the predatory behavior the letters referenced were fakes, traceable to News Corp lawyers or others working for Murdoch, who owned Facebook’s biggest competitor, MySpace. “We traced the creation of the Facebook accounts to IP addresses at the Apple store a block away from the MySpace offices in Santa Monica,” the executive says. “Facebook then traced interactions with those accounts to News Corp lawyers. When it comes to Facebook, Murdoch has been playing every angle he can for a long time.” (Both News Corp and its spinoff 21st Century Fox declined to comment.)
Got that? Facebook actually traced fake accounts, that were handed to long-grandstanding anti-internet crusader Richard Blumenthal (then a state AG, now a Senator) back to News Corp. And Murdoch strongly implied to Facebook execs that he needed to get a better deal from them or his publications, such as the WSJ, would put out hit pieces.
So, yes, there are legitimate points of concern to raise about big internet companies. I'm not one to normally believe in cynical conspiracy theories, but it's not at all crazy to think that the recent onslaught in major media properties may not be coming from the most ethically sound place. After all, if Hollywood has plotted in the past to do exactly that, why would anyone expect them to have given up those underhanded games?
Permalink | Comments | Email This Story