|
submitted by /u/digicat to r/computerforensics [link] [comments] |
Heath Leach
Shared posts
Windows Incident Response Cheat Sheet
Decrypting SSL/TLS traffic with Wireshark
Introduction The Internet wasn’t designed to be secure from the start. Many protocols (such as HTTP and DNS) were designed to serve their purpose of conveying information over the network without spending time on security. However, in the modern Internet, privacy and security are major priorities. As a result, the Transport Level Security (TLS) protocol […]
The post Decrypting SSL/TLS traffic with Wireshark appeared first on Infosec Resources.
Decrypting SSL/TLS traffic with Wireshark was first posted on June 18, 2019 at 8:03 am.
©2017 "InfoSec Resources". Use of this feed is for personal non-commercial use only. If you are not reading this article in your feed reader, then the site is guilty of copyright infringement. Please contact me at darren.dalasta@infosecinstitute.com
How to get caught by Fallout76's anti-cheat
 |
submitted by /u/Douggem to r/REGames [link] [comments] |
.NET network trace - Collects network traces of .NET applications.
 |
submitted by /u/owen800q to r/csharp [link] [comments] |
Circle City Con 2019 Videos
These are the Circle City Con videos. Thanks to the staff for inviting me down to record. Big thanks to @irishjack, @TheHomoHacker, @Paint27, @songsthatsaved, @nogoodrobot, @kitwessendorf, @cxstephens, @uncrustabl3 and others for helping set up AV and record.
Data Access Rights Exploits under New Privacy Laws
Amber Welch
How to reach and teach youth about Cybersecurity (if anybody will let you)
Jason Smith
More Tales from the Crypt...Analyst
Jeff Man
Could Static Code Analysis and Secure Coding have Saved the Death Star?
Mary Waddick
I’ll Complete My Threat Model Later Mom!: Infosec in Middle School.
Ashley Benitez Smith
Cons & Careers
Steven Bernstein
3D printing canister-launchable drones for city-scale wardriving
Glytch Tech
The Hunter Games: How to find the adversary with Event Query Language
Ross Wolf
Star Wars: How an ineffective Data Governance Program destroyed the Galactic Empire
Micah Brown
Security lessons from the Woofmutt…
Chris Roberts
What The Frida Gave Me: A Novel Take on E-Ticket Forging and E-Ticket Stealing
Priyank Nigam
(Not Recorded)
Get off my lawn… or are we looking for the right people?
Mike (Shecky) Kavka
Endpoint Security, Swimming Through the Snake Oil
Dan Beavin
Do You Have What It Takes? How to Support Your Career From Community Involvement
Kathleen Smith
Catching the Guerrilla: Powershell Counterinsurgency
Aaron Sawyer
Standardizer: a standardization framework for your security alerts
Christian Burrows
Call Of Duty, Modernest Browser Warfare v2
Dhiraj Mishra
(Did not happen)
Information Security Practice Principles a Rosetta Stone for information security work
Susan Sons
What Can Data Science Do for Security?
Wendy Edwards
Deepfakes: If anything can be real then nothing is real
April Wright
(Not Recorded)
Evicting the Password from the Digital Estate
Alex Chalmers
A Theme of Fear: Hacking the Paradigm
Catherine Ullman
Beginning DFIR - How to get started with Cooties
Lisa Wallace
Of CORS it's Exploitable! What's Possible with Cross-Origin Resource Sharing?
Rebecca Deck
Nexus Zeta - How a newbie hacker managed to create a monster botnet
Adi Ikan
5G: Security Pitfalls and Considerations
Swapnil Deshmukh
(Did not happen)
Training and Education for the New Realities of Privacy and Security
Mitchell Parker
Container Security Deep Dive
Yashvier Kosaraju
Hacking Humans: Addressing Vulnerabilities in the Advancing Medical Device Landscape
Gabrielle Hempel
One Random Insecure Wep Application Please (ORIWAP)
Nancy Snoke
an Implantable Computer
Doug "c00p3r" Copeland
Modern AppSec Gotchas
Fletcher Heisler
A Few Things Right: Insights from Live and Simulated Incident Response
Chad Calease
The Resilient Reddit C2
Zach Zenner
F! Attribution
Xena Olsen Jared Peck
Inside Out Security - Building Castles not Warehouses
Alyssa Miller
Failure Is Not an Option: Developing Realistic Disaster Recovery Tests
Colin Campbell
Wibbly Wobbly: Designing Security for Systems that are Bigger on the Inside
Wolfgang Goerlich
How I was able to access AWS credentials by first finding an unusual redirection then getting kind of Remote File Inclusion (RFI), escalating it to Server Side Request Forgery (SSRF) and finally getting hold of AWS EC2 Credentials.
Code Analysis of Basic Cryptomining Malware
 |
submitted by /u/kindredsec to r/blackhat [link] [comments] |
microsoft/SymCrypt: Cryptographic library used by current versions of Windows
POC of CVE-2019-0708 (Not Weaponized)
 |
submitted by /u/netsec_burn to r/blackhat [link] [comments] |
CVE-2019-0708: A Comprehensive Analysis of a Remote Desktop Services Vulnerability
Setup and Debug JavaScriptCore / WebKit
 |
submitted by /u/LiveOverflow to r/LiveOverflow [link] [comments] |
Electro music website
I remember a liveoverflow video where he mentions a cyberpunk looking website with like albums of electro music. Anyone can help me find that? It was amazing.
PS: Sorry for my sloppy description that's pretty much all I remember
[link] [comments]
Your company is socially engineering you to increase your loyalty and maximize your output
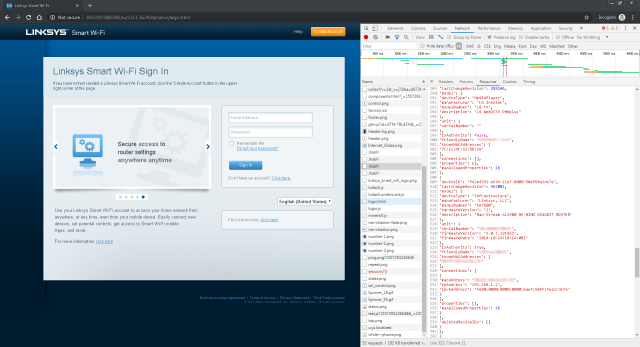
>20,000 Linksys routers leak historic record of every device ever connected

(credit: US Navy)
This post has been updated to add comments Linksys made online, which says company researchers couldn't reproduce the information disclosure exploit on routers that installed a patch released in 2014. Representatives of Belkin, the company that acquired Linksys in 2013, didn't respond to the request for comment that Ars sent on Monday. Ars saw the statement only after this article went live.
More than 20,000 Linksys wireless routers are regularly leaking full historic records of every device that has ever connected to them, including devices' unique identifiers, names, and the operating systems they use. The data can be used by snoops or hackers in either targeted or opportunistic attacks.
Independent researcher Troy Mursch said the leak is the result of a flaw in almost three dozen models of Linksys routers. It took about 25 minutes for the BinaryEdge search engine of Internet-connected devices to find 21,401 vulnerable devices on Friday. A scan earlier in the week found 25,617. They were leaking a total of 756,565 unique MAC addresses. Exploiting the flaw requires only a few lines of code that harvest every MAC address, device name, and operating system that has ever connected to each of them.
Introduction to Networking | Network Basics for Beginners - VPN Tunneling
New Series: Getting Into Browser Exploitation
 |
submitted by /u/LiveOverflow to r/LiveOverflow [link] [comments] |
NolaCon 2019 Videos
Recorded at NolaCon 2019. Thanks to @CurtisLaraque, @mikearbrouet, @openbayou, @takanola, @therealmacjeezy, Jason, Cole & @klulue for the video recording help, and @nola_con, @erikburgess_, @NolaConYvonne & Rob for having me down to record.
One Random Insecure Wep Application Please (ORIWAP)
Nancy Snoke
Understanding XSS
Christina Mitchell
DNS - Strategies for Reducing Data Leakage & Protecting Online Privacy
Jim Nitterauer
Automating Hashtopolis
Evil Mog
"It's Malware Time" - A Bar Crawl from Skunked Homebrew to Rotten Apples
Erika Noerenberg
Breaking into Cyber: How the hell are you supposed to get started?
Josh Millsap
Making an internal Let's Encrypt relay server
Josh Harvey
Keynote - I PWN thee, I PWN thee not!
Jayson E. Street
Formula for a Bug Bounty Program
Chris Holt
Forensics Phish Tank: Breaking Down Analysis of Advanced Phishing Emails
Joe Gray & Sophia Fadli
Baking Your Anomalous Cookies
Jim Allee
Waiter, there's a compiler in my shellcode!
Josh Stone
Empathy for the (Devel)oper: Lessons Learned Building An Application Security Module
Yolonda Smith
MORE Tales From the Crypt...Analyst
Jeff Man
IR with Volatility Framework
Evan Wagner
Let's Talk About WAF (Bypass) Baby
Brett Gravois
Behavioral Security and Offensive Psychology at Scale
Josh Schwartz. Samantha Davison
My making of a Metasploit Module
Aaron Ringo
Don't Panic! A Beginner's Guide To Hardware Hacking
Phoenix Snoke
The Jazz Improv of Infosec
Damon J. Small
Elliptic Curve Cryptography: What it is and who needs it
Michele Bousquet
Introduction to Networking | Network Basics for Beginners - VPN Protocols (IPSec)
Here is the third installment in my ghidra tutorial series. This is about solving an intermediate crackme
 |
submitted by /u/RayofLight-z to r/hacking [link] [comments] |
Damn Vulnerable Crypto Wallet - An extremely insecure Ethereum cryptowallet
Linksys Wi-Fi Routers are vulnerable to leaking information about connected devices.
 |
submitted by /u/_TjBrett_ to r/hacking [link] [comments] |